FluBot has built up a community of compromised Android phones in the UK since April and in the past 24 hours has commenced monetising them by sending overlays for British Banks.
FluBot first appeared in 2020, targeting mainly Spanish banks, but recently it has spread its reach, with Australian, German and Polish banks all affected within the last few weeks. UK banks are now firmly in its sights, with HSBC and Santander the first to be affected, and Lloyds and Halifax following shortly after.
How FluBot works
FluBot spreads via SMS messages often purporting to be from a delivery company, alerting the recipient of an upcoming delivery and inviting them to track the parcel by clicking a link in the message. Other times, the SMS may pretend to be a voicemail notification, with a link which the recipient is told to follow to hear the message. This link takes the victim to a lure page hosted on a compromised web server, from where the user is prompted to install the malware on their mobile device.
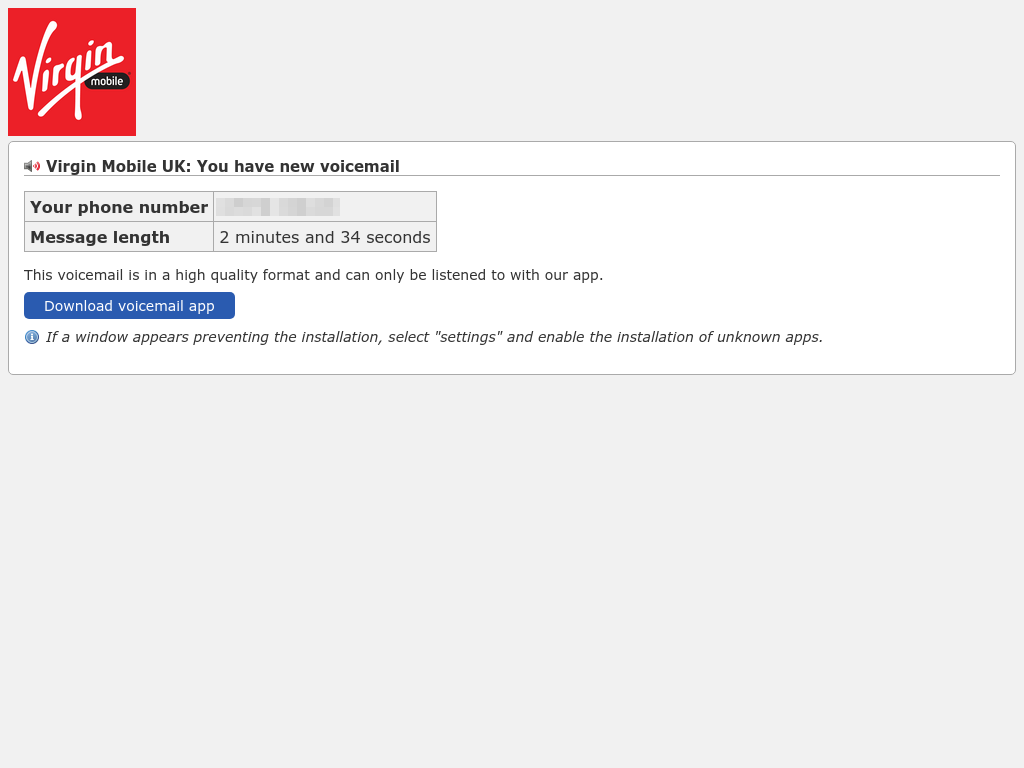
A fake Virgin Mobile lure page asking the user to download a ‘voicemail app’
Once installed, the malware asks the user for various permissions, including the ability to draw over other apps and to read the user’s contact list, which it uses to find new people to spread to.
The malware periodically contacts the C2 (command and control) servers with a list of the apps on the user’s device. The servers respond with the subset of them which are targeted, from which it will download available overlays, which look like the genuine apps’ login screens. It then displays these on top of the apps when they are opened, tricking the user into entering their account details, which are sent back to the C2 servers to be used nefariously.
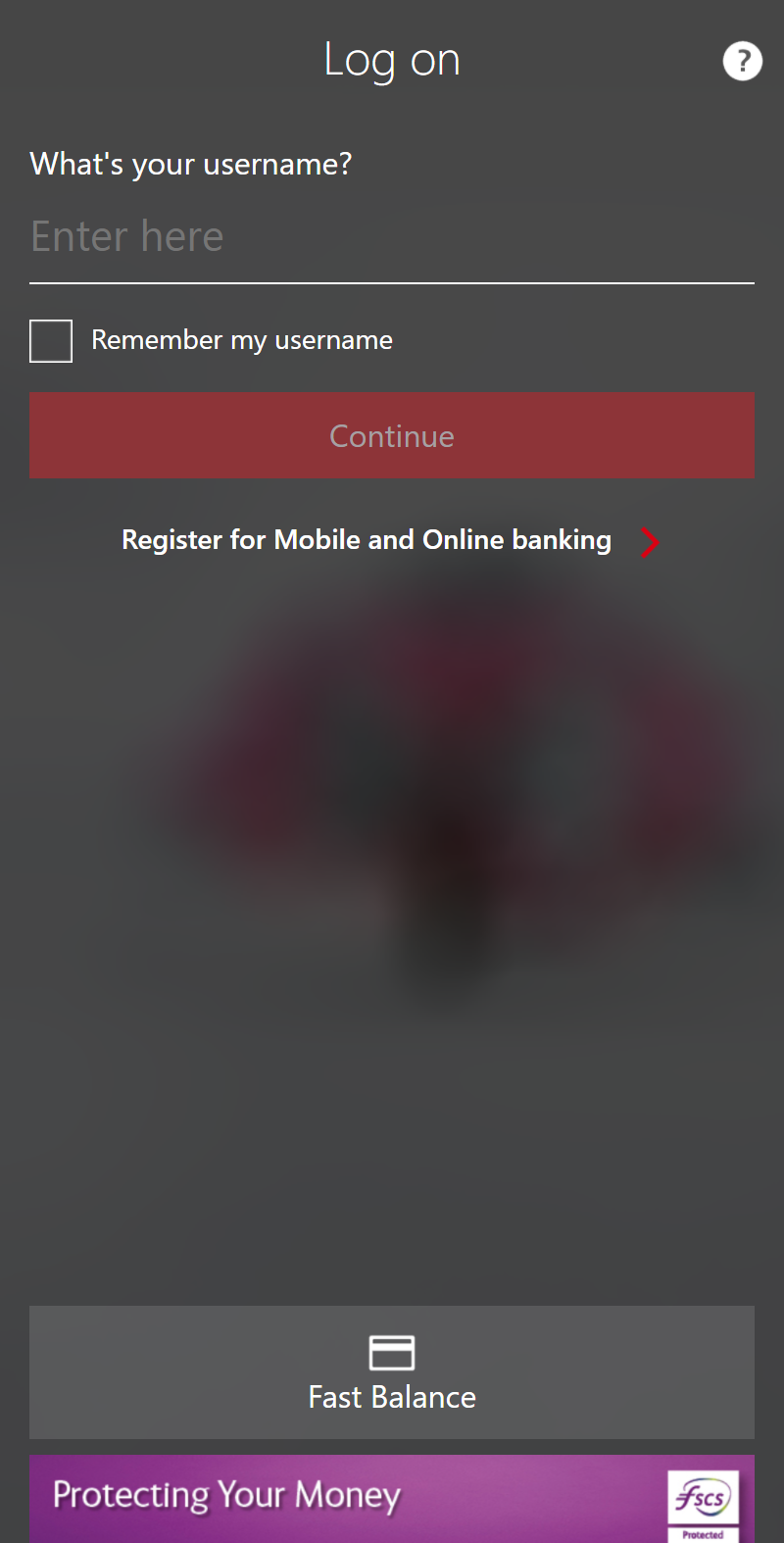
FluBot overlay for HSBC
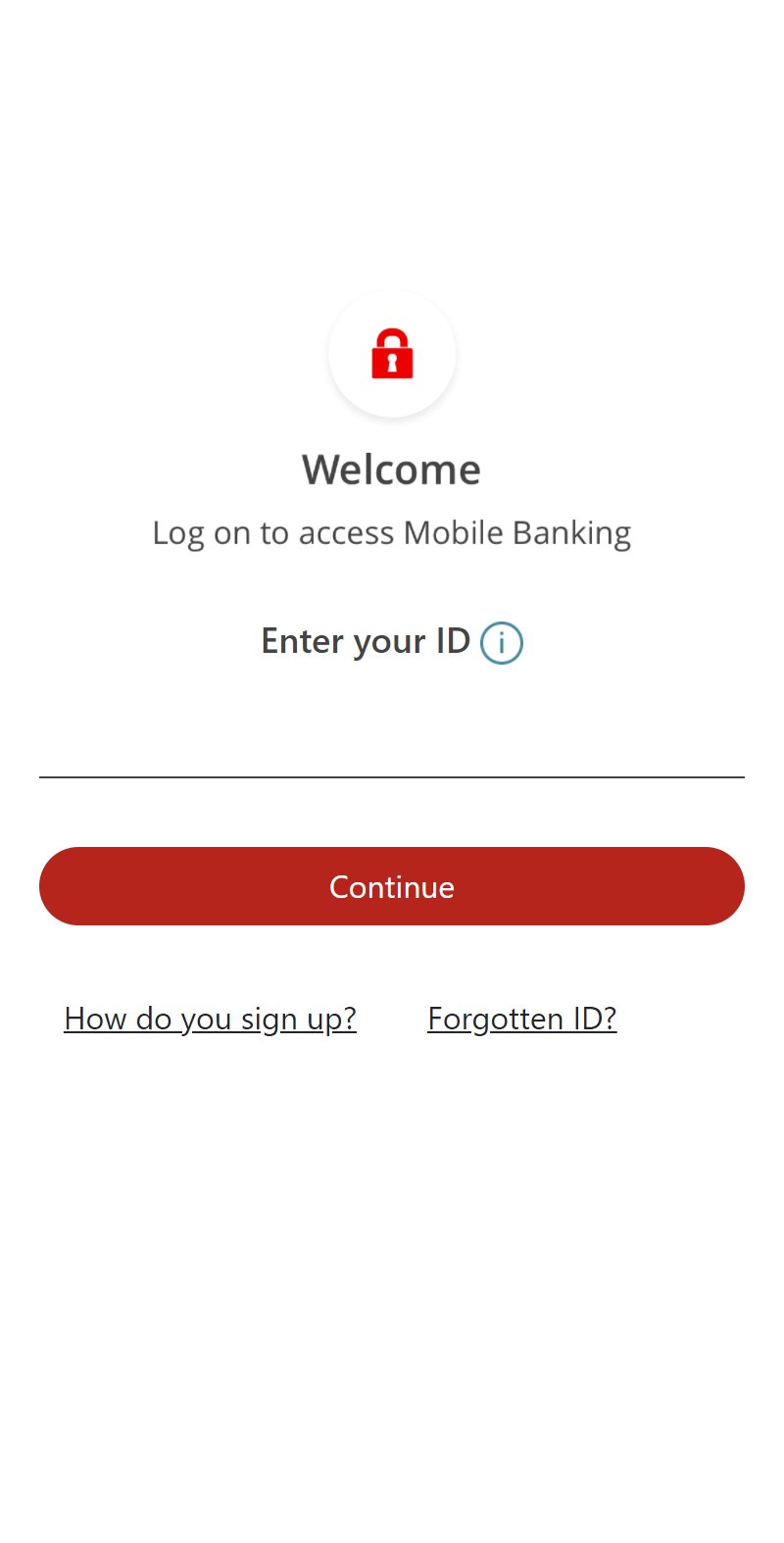
FluBot overlay for Santander
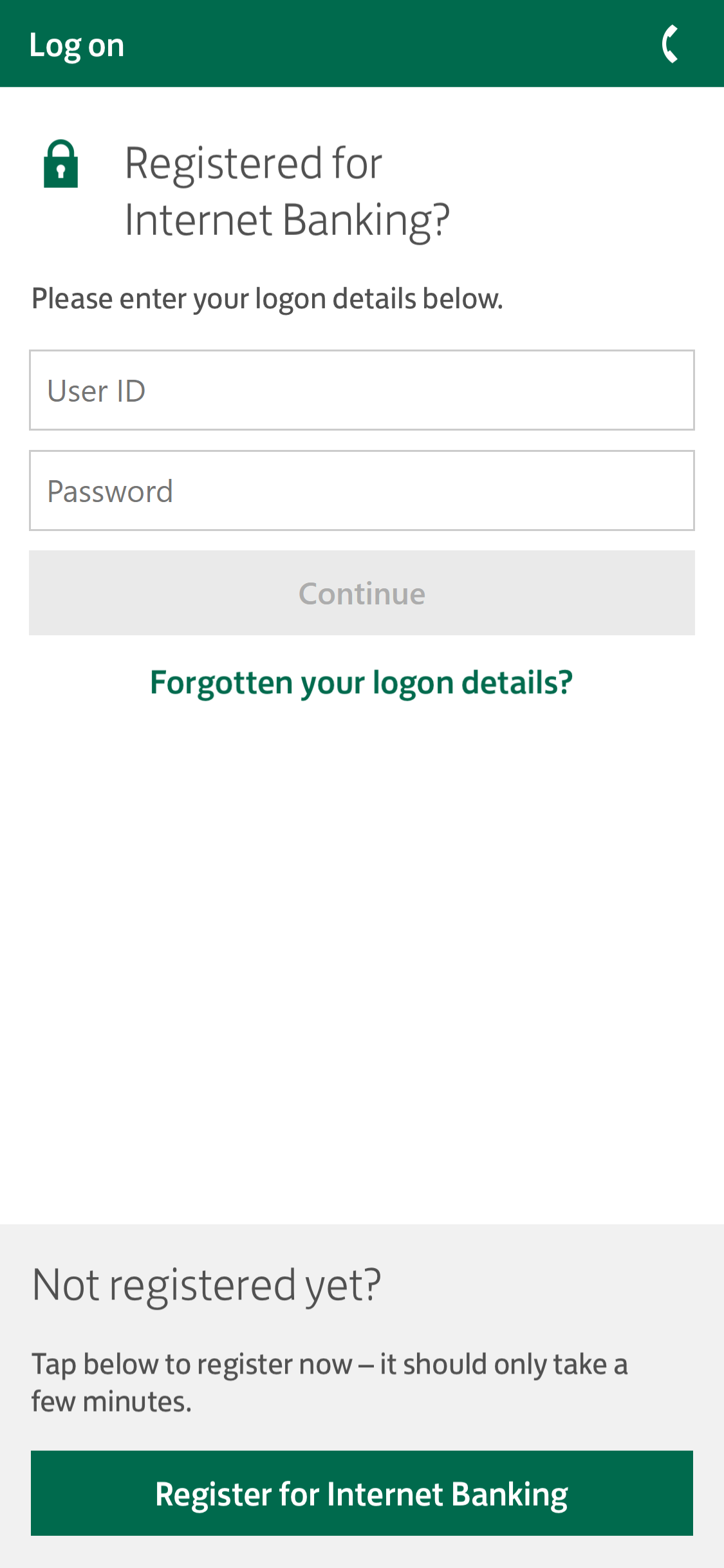
FluBot overlay for Lloyds
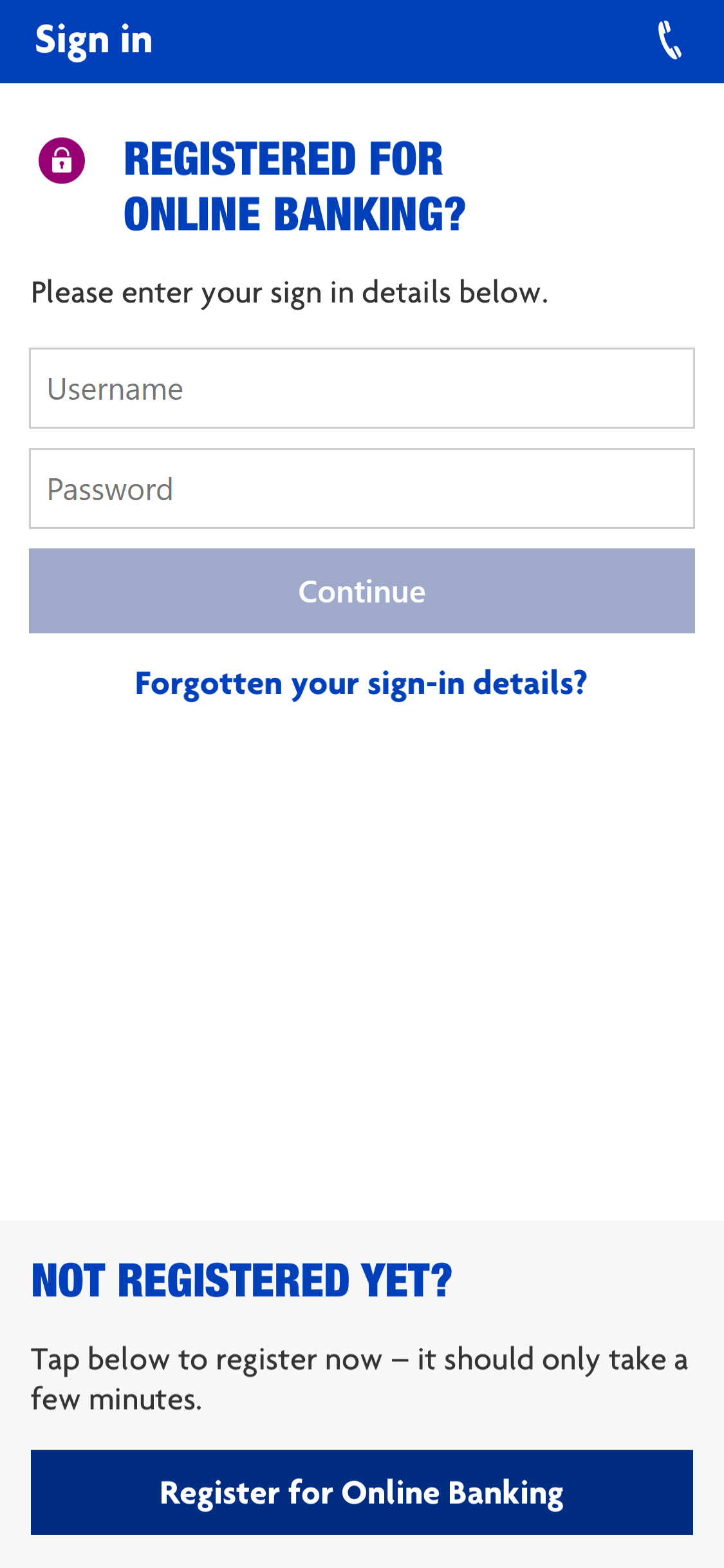
FluBot overlay for Halifax
Countermeasures
Android users can protect themselves from FluBot using the Netcraft Android app, which will block any connections to the lure sites and so prevent the malware from being installed in the first place. Banks and mobile networks can protect their customers through a range of countermeasures provided by Netcraft.